PC Security in a Connected Environment
Roy Schestowitz
University of Manchester
Overview
- Initial paths to security
- firewall setup
- frequent updates
- virii/worms/Trojans protection
- Safer computer 'lifetime'
- maintenance tasks
- cautious installations
- spyware purging
Firewall: The Essence
- Prevent communication from unauthorised sources
- When firewall disabled, malicious operations can be invoked from outside
- When enabled, the possibility of interference with applications arises
- Good firewall filters out the malicious, yet does not conflict with applications
Firewall: Specifics
- Passive
- does not require any action from the user
- with some operating systems e.g. Linux - built onto the kernel (core)
- Windows XP - Service Pack II (Windows update) incorporates it
- Active
- Windows 2000 - ZoneAlarm and the like, third-party solutions
- Linux and Mac (Linux-related) - usually just passive, only minor threats
Patching up the Operating System
- Operating systems are often released with vulnerabilities
- When vulnerabilities are discovered, patches (updates) get distributed
- Passive updates
- updates are downloaded and installed in the background
- Semi-passive
- user prompted to get a patch - must always accept
- Active
- user needs to periodically check if patches/fixes exist
- in Windows,
Start»Windows Update
Anti-virus
- Virus attacks had a comeback in recent years
- 'Programs' that damage the state of the operating system
- Vandalistic exploitation of badly-designed programs
- Combatting virii:
- switch off/disconnect computer when unused
- keep Anti Virus (AV) software up-to-date
- purchase AV with care, free solutions exist
- most necessary when using Windows
- Windows prime target because it is the most prolific operating system
Anti-virus and Platforms
- Big threat, especially to Windows (danger involves port scanning)
- Linux and Mac are claimed to be much safer than Windows
- Mac - almost no virus ever found 'in the wild'
- Linux usually immune to attacks (in practice, not realistically) without any add-on software
- Windows 98 seems to be no longer attacked
- Windows 98 is a minority, but still not secure
Anti-virus - Continued
- Windows 2000, NT and ME: among the prime victims
- Windows XP and 2000+ must be patched
- Support by Microsoft discontinued - users become liable
- Keep an eye on the news
- Recent wave of vulnerabilities crippled many networks and caused disaster
- 3 points to remember: (1) Firewall, (2) updates and (3) AV
Frauds, Phishing and Spying - E-mail as Source of Attack
- Bulk of E-mails that are not reliable
- Never include passwords, PIN numbers, etc. in an E-mail
- Messages are easily readable by anyone in between you and the receiver
- Share password via phone; mobile phone safer than landline
- Encrypted mail - difficult to set up and must be supported by recipient
Frauds, Phishing and Spying - E-mail Address Protection
- Avoid disclose of E-mail address unless no other choice remains
- Especially abstain from E-mail disclosure in Web-based/electronic forms that are questionable
- Addresses get harvested, put on CD's, then sold by the millions
- Obfuscate addresses, e.g.
jimREMOVE_SPAM@man.ac.uk - E-mail addresses should be readable to humans, not harvesting 'robots'
Frauds, Phishing and Spying - Spam
- Spam (bulk mail) leads to susceptibility to attacks
- Filters can easily weed out fraudulent messages
- If not using professional address, instantiate an account with filters built-in
- Google Mail appear to offer the strongest spam filters
- Filters are based on behaviour of all Google Mail users (collaborative spam flagging)
Applications Security

- Internet Explorer not as safe as Mozilla Firefox or Opera
- Keep browser/s up-to-date
- Netcraft Toolbar (shown above) - displays risk level for sites
- Avoid installation of software or plug-ins
- Programs and obscure functionalities tend to "get a home" alongside other programs
- Add-ons affect speed, promote spying on surfers
E-mail and Security
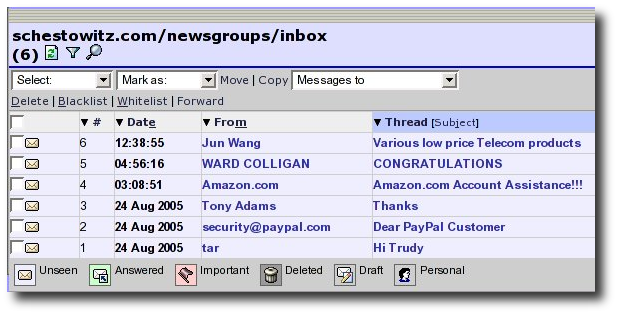
E-mail and Security - General Advice
- Password theft and frauds
- Phishing - malicious sites, tricky pop-ups
- Credit card details - handle with care
- Always check source of Web pages
- Identify full postal address (otherwise a red flag should be raised)
Performance Perils
- Windows Registry - do not allow bloating
- Installation of one program 'invites' another
- Integrity checks (e.g.
Scandisk) and filesystem maintenance (e.g.Defrag) - Alteration or corruption of settings
- Spying - to result in targetted ads pop-ups
Final Message
- Set up a firewall
- Update the operating system
- Run anti-virus software
- Use trusted/reliable applications
- Avoid excessive installations
- Be alert when checking E-mail