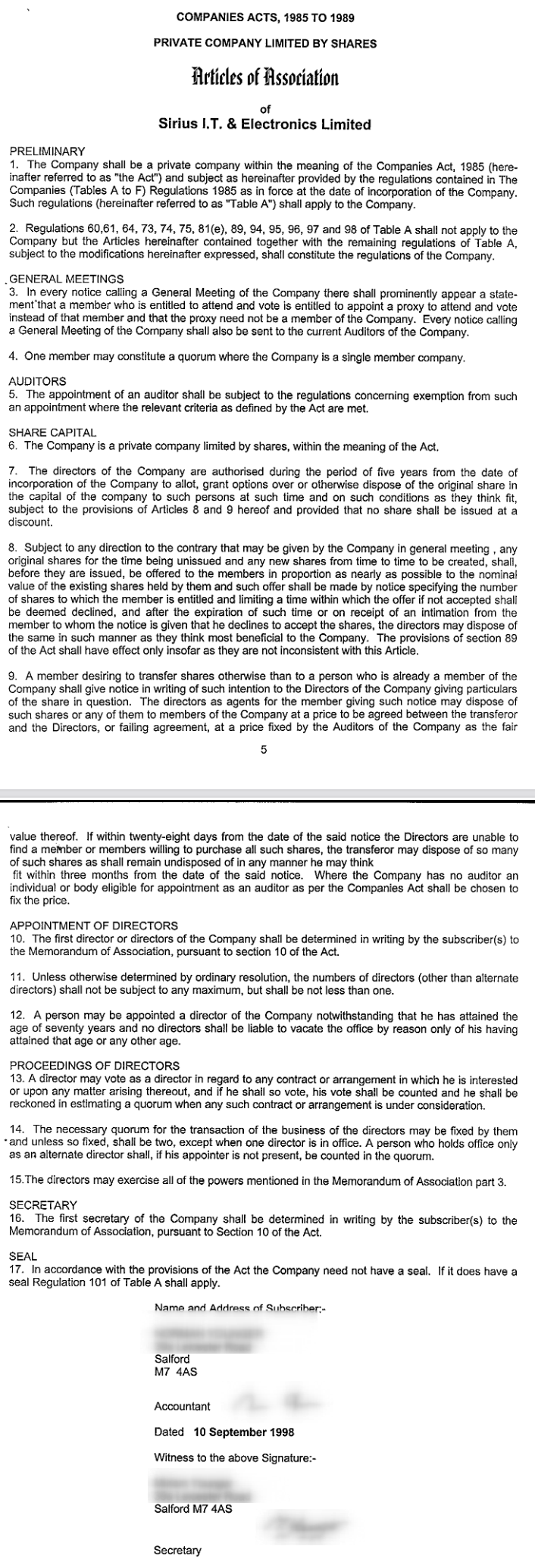
Date: Tue, 30 Aug 2022 09:00:50 +0100
MIME-Version: 1.0
User-Agent: Mozilla/5.0 (X11; U; Linux i686; en-US;
rv:1.7.6) Gecko/20050317 Thunderbird/1.0.2 Mnenhy/0.7.4.0
From: Roy Schestowitz
Subject: Handover to Shift 2 (30/08/22)
To: [whole team]
[...]
https://www.darkreading.com/cloud/lastpass-data-breach-source-code-stolen
users need to change all the passwords they have
there and not keep them there if they value real
security not paper mills.
Summary: Sirius ‘Open Source’ failed to protect its clients. While in Sirius I’ve been warning management about this for 4 years; all I received for these warnings was a bunch of threats against me (for raising and politely bringing up the subject).
TODAY is a holiday here, but the subject cannot be left aside. The saga cannot be paused because the holidays are being exploited by truly nefarious companies for cover-up.
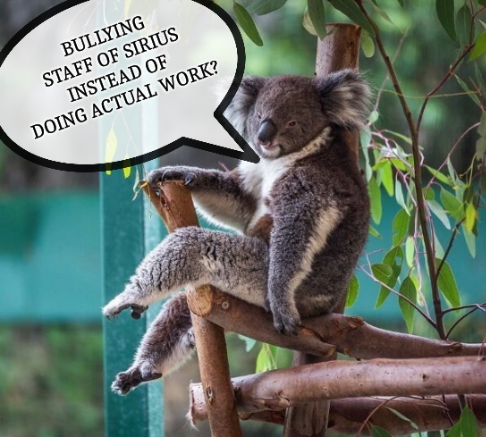
Those who are following Daily Links may have noticed already that there are further admissions of a breach at LastPass; mind the timing… just before the most major holiday, probably by intention (it’s a well-known Public Relations or “disaster mitigation” strategy).
We’ve decided that it would be better not to surrender to such “strategic timing” tricks. The revelations were scheduled to be accompanied by PR, complete with “waffle” and face-saving lies (postponed for months… to be explained much later). Suffice to say, in the case of security breaches, people must be informed as soon as possible so that they can take action. But not so with LastPass! It would not be the first company to do so. They just wish to say they said something (without anyone truly noticing), at least in retrospect. It’s in-hindsight optics.
But this post isn’t primarily about LastPass itself; it is a bigger blunder that a company which calls itself “Open Source” actively outsourced away from Open Source to this highly untrustworthy company. The CEO of “Sirius Open Source” [sic] was even trying to defend all the LastPass lies, just as he doubles down on his own lies routinely. He is a pathological liar, so he can probably relate to those who do the same at LastPass.
What we’re seeing at LastPass is just face-saving admissions to clean their hands and claim they were “transparent” and complied with the law (to avoid fines/penalties). But we might not see much press coverage about this; journalists (what’s left of them) are already on holiday. The editors won’t pick any stories from them, no matter how important or urgent those stories may be. Heck, not many people will read the news, either!
As we shall show, in light of more incidents and few reports (far too few), the time to cover this is tonight, not next month as expected/scheduled.
LastPass has certainly failed, but so did Sirius. Sirius cannot claim to be a passive victim here!!
Sirius was picking on the people who reported that LastPass had suffered a security breach and wanted to do the right thing about it. That’s me. In this particular case it’s not the fault of another company but the fault of Sirius for putting all the passwords “in the cloud” in spite of repeated warnings from its long-serving and loyal staff. Honest staff.
Having cautioned about LastPass, which had already suffered breaches, I was repeatedly threatened in video calls for doing what’s right. Of course those video calls were done using proprietary software — that’s what Sirius was becoming. Of course they said I’d receive a copy of the recording but never received any! At Sirius, the lying and deceit had become routine, they ultimately became the norm. In a company where about half the staff goes by the name “manager” the only way to progress was to participate in the lying.
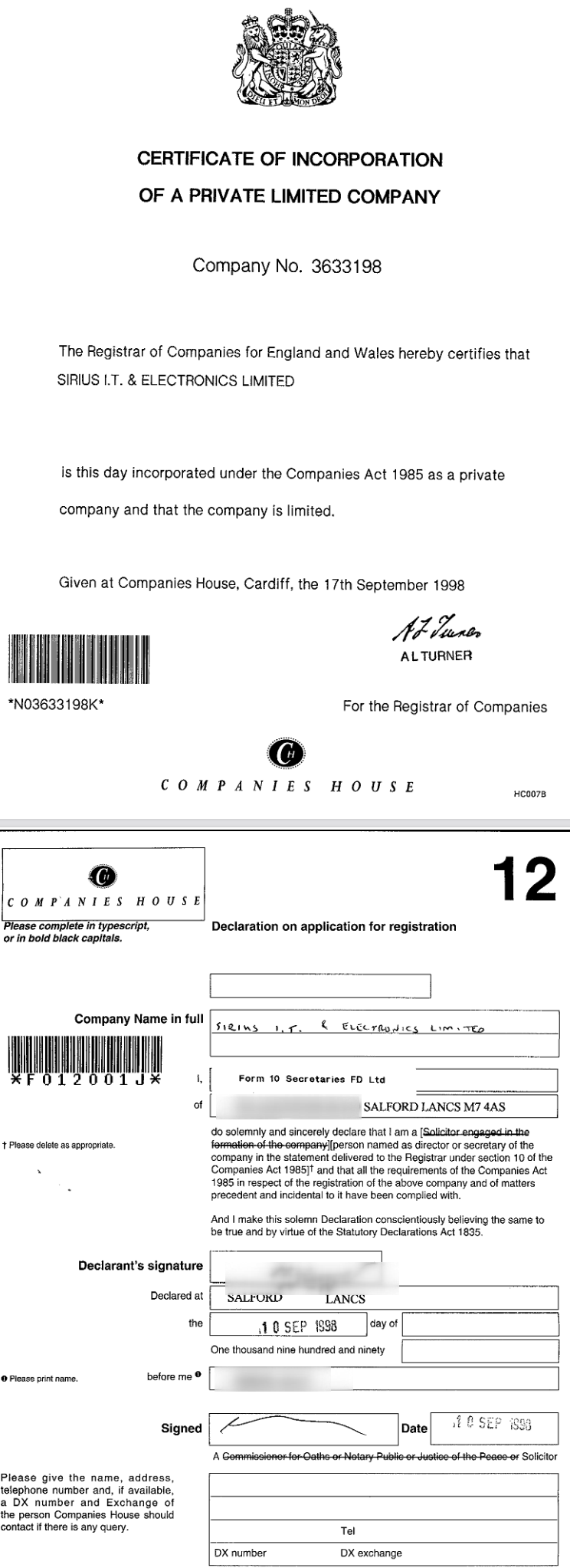
So what happens now? Well, Sirius could get sued by the clients, not just asked for a refund, for misinforming and neglecting systems, even abusing people who cautioned about this internally. I don’t intend to contact clients personally, but maybe they will realise this regardless (by serendipity). What about ISO? Will it revoke certifications? We’ll cover this in a separate part next month.
Do not expect much press coverage about LastPass, owing partly to timing. From the latest Daily Links:
-
If you have a LastPass account you should have received an email updating you on the state of affairs concerning a recent LastPass breach. While this email and the corresponding blog post try to appear transparent, they don’t give you a full picture. In particular, they are rather misleading concerning a very important question: should you change all your passwords now?
-
During the recent LastPass breach, it was finally revealed that the password vaults were leaked. The company is still downplaying this, but the time to take action is NOW.
I cautioned about this internally about half a dozen times (the LastPass breaches alone), but nothing was done by any of the managers. So they’re all culpable. They all failed to act. One of them, who lies routinely, said that according to LastPass, LastPass is OK and things are safe. They’re just lying to everyone, like he habitually does. Cover-up basically.
Sirius is a disaster, it is a catastrophe, and it’ll never admit it. So someone needs to say this out loud. They’re probably still covering up for Sirius and its misguided use of LastPass, strictly hiding it from most of the clients (as usual).
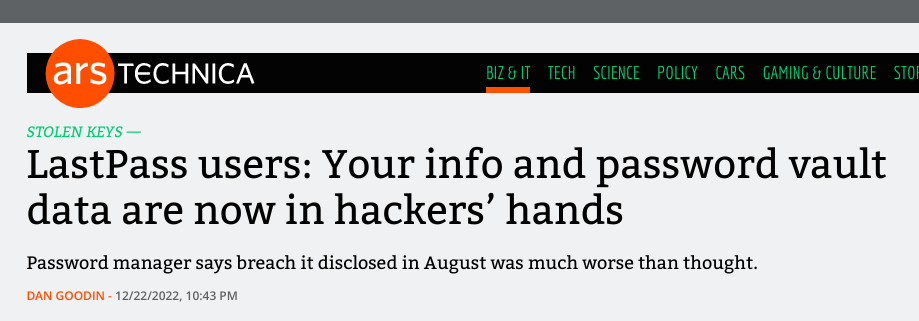
My latest warning about LastPass came about 1-2 days before I left the company. I reproduce my full message below, but bear in mind that some of the pertinent details will be shown next month when we’re done with the report and move on to bigger issues:
Hi,
I’ve been receiving some relatively solid and professional legal advice for several weeks already. To put it quite bluntly, the impression legal professionals get is that the company cannot afford lawyers and thus makes wild guesses, based on a gut feeling at best.
In Rianne’s case, the allegations are shockingly weak. This, in turn, makes the trail of correspondence work very strongly in our favour. We’re not impulsive, we just follow the law. We’ve both followed the law all along. We know our rights and we have people to assess the law.
The latest invitation is legally problematic for several distinct reasons. It would not constitute a fair ‘trial’, on a number of different grounds. What you’re trying to apply here is the controversial Reid method, which isn’t just notorious but also unlawful in some jurisdictions. No proper protocols and procedures were followed until (probably due to a lack of legal advice) more recently. In fact, “Investigation Meeting” suddenly and disingenuously became “Disciplinary Hearing”. The process embarked upon did not respect the employee’s right to privacy (setting out the importance of confidentiality) and it seems to be more of a personal vendetta than a real, justifiable case.
Regarding any such hearing, where possible the employer should get somebody who’s not involved in the case to carry out the investigation, for example another manager or someone from HR. HR does not exist in Sirius per se, so the company needs to contract outwards, just like several years ago where HR sided with us, not with the harasser in chief. We never received an apology after that incident. And moreover, I wish to make it known that I am referring to a single example of many such incidents. I can elaborate later.
The sudden and very much unprovoked-for suspension is problematic on a number of legal grounds. There’s consensus among legal professionals (visited or spoke to several) that it was inappropriate and over the top. Perhaps the purpose of it was to obstruct the accused from accessing defensive/supportive evidence. There’s no reason for a suspension of someone who for 12 years never ever did something “dodgy” to company or client assets; quite the contrary. Unless the employer thinks there is a risk that the employee might tamper with evidence or influence witnesses, a suspension is entirely unnecessary. I have no history of tampering with evidence or influencing witnesses. In fact, the “evidence” presented (only a fortnight later!) is actually controlled by me rather than the company. The IRC logs are very informal and have nothing to do with Sirius.
There is also consensus that what’s proposed constitutes a kangaroo court and the reason you don’t want an independent HR agency to handle this (like before) is that the case will be thrown out with prejudice and the company may be held accountable for a lot more than just frivolous accusations and moral damages (twofold).
On deciding whether to suspend an employee, there are also clear legal guidelines. If there’s a serious issue or situation, an employer might consider suspending someone while they investigate. But in this case, the nature of the accusations makes it abundantly frivolous. An employer should consider each situation carefully. Suspension will only be needed in some rather rare situations. This is why, right from the very beginning, the letters and demands sent were legally invalid. If an employer feels they need to suspend someone, it’s important to consider alternative options to suspension and the wellbeing of the person they’re thinking of suspending (unless the intention is to shock and seek reprisal). The employer should think about who will handle matters if further action is needed, but in this case it seems like one or two person control the process from beginning to end. Where possible, a different person should handle each step of the disciplinary procedures: the investigation, the disciplinary hearing and outcome, and the appeal hearing (if an appeal is raised).
It might moreover be useful to document (e.g. write in great length) and to show a clear, systematic pattern; I can prove and neatly present a pattern of evidence which points to the actions by the CEO being vindictive. It would not be unprecedented either. Expect a 50-page report quite soon. A legal team is looking into it.
The process has in general been a travesty and a potential source of disgrace to the company. In this particular case, someone acting as a judge for oneself is not looking good. In principle, recusing oneself is one option, but the process is already tarnished by irregularities that hamper any perception of objectivity and fairness.
This is not a good way to end a relationship with the company. It didn’t have to end like this.
A good company values its workers, listens to workers, instead of treating them like enemies to be deceived and marginalised. Apropos, only minutes ago:
https://techcrunch.com/2022/11/30/lastpass-goto-breached-customer-information/
If only someone kept warning that LastPass was trouble…
That “someone” was only ever me, raising the alarm like half a dozen times. I still have copies of messages warning against this. Or reporting the incidents spotted in LastPass (at the time LastPass was gaslighting the reporters).
Remember that LastPass wasn’t just adopted to store Sirius account credentials; clients’ credentials (for full access to machines) were outsourced to LastPass, likely without their knowledge. In other words, if LastPass breaches resulted in breaches of customers’ systems, they might not even know it was the fault of Sirius. They might not know passwords of theirs ended up in LastPass.
Here are more recent reports (around the time I left) about the breach:
-
LastPass, a major password manager, says it has suffered its second breach in three months by the same unauthorized party.
-
Was the security breach of LastPass limited? In its official statement, the company said that the breach was limited to the development environment and couldn’t reach the customers’ data and encrypted passwords. The company didn’t specify what information was accessed as the investigation is currently ongoing. It further stated that the production environment lies in a different physical environment than the development environment.
-
In this video, we check an article on how the world-leading password manager, LastPass, became the victim of a security breach again. LastPass is owned by GoTo and boasts over 25 million users, and serves around 80,000 businesses worldwide.
The denials from LastPass were basically lies. It doesn’t matter how many facts one presents to Sirius management, it’ll still never admit mistakes and move to something safe, self-hosted, and “Open Source” (like the company’s name). Passwords used to be stored in a wiki (Foswiki) behind a VPN and it was initially self-hosted. Better solutions exist now, e.g. Bitwarden. As this weeks-only coverage from “It’s FOSS” put it, “Bitwarden gets better every day, making things more convenient.”
Sirius could use Bitwarden or many other things.
It’s not about a lack of features; it’s about a lack of real leadership in Sirius. Bitwarden has a lot of good features. To quote the above: “Bitwarden is easily the most popular open-source password manager right now. It is simple to use, cost-effective, conveniently available on mobile/desktop, and secure enough for most common use cases. While it already supported passwordless authentication techniques like fingerprint sign-in, Face ID, PIN, on mobile/desktop, it now has a new addition.”
Sirius also rejected FOSS for communications, despite several members of staff pushing for FOSS and volunteering to install FOSS. Lip service isn’t enough.
To quote the CEO would be worthless (no point pasting E-mail) because he responded with no substance, only a link that parrots lies from LastPass itself.
In spite of this apathy, the subject was again mentioned in handovers and various other means, not just E-mails, only to be dismissed or ignored. If clients lost or lose (or will lose) control of their systems, Sirius is likely to blame. Some crackers out there probably have a list of all the passwords of all the important machines of clients, sometimes even private keys!
This is what happens when companies implement “Mickey Mouse” security and clients trust such “Mickey Mouse” companies to manage their critical systems.
Sirius is of course still not interested in facts or actual news. Expect Sirius management to dismiss the latest revelations as not important and resort to defamatory ad hominem against the messengers, i.e. the usual.
It’s worth noting that, from a purely legal point of view, we didn’t even inform the clients about: 1) the breach; 2) the passwords being there, possibly without their knowledge or consent.
The issues go far further than password management, but LastPass is what’s in the news right now. It’s worth adding that Sirius uses LastPass in ways it ought not be used, e.g. if they are setting up a new client in OTRS they send the password to LastPass (via LastPass to client). “Mickey Mouse” all over this thing!
Some time next month we’ll cover “Communication Tools” at Sirius and how much further the privacy/security failure goes.
Screenshot credits: LastPass Password Vaults Stolen By Hackers-Change Your Master Password Now – Forbes, LastPass users: Your info and password vault data are now in hackers’ hands – Ars Technica, Hackers stole encrypted LastPass password vaults, and we’re just now hearing about it – The Verge






 Filed under:
Filed under: