Palm and Password Management
 ike many others, I keep every password stored in my Palm. Virtually any username, password and network address which I must remember will be located under one category or another in electronic form.
ike many others, I keep every password stored in my Palm. Virtually any username, password and network address which I must remember will be located under one category or another in electronic form.
Quite a long time ago I discovered, much to my surprise, that others use the exact same methods as me for storing passwords. This was not the case since they were influenced by somebody else, but simply because it seemed like the right thing to do; it came naturally. Most recently, it was a technologically-oriented lady whom I noticed ended up storing her passwords in the exact same fashion as me. This begs the questions: does every Palm user adopt the same habits? And if so, was it self-taught?
 No doubt there is a certain pattern — a certain adaptable method. Many start off by entering various scattered password into a single password-protected memo (the ‘piece of paper in the drawer’ equivalent). As experience develops, time takes its toll and scale becomes an issue. Passwords begin to migrate to the address book, possibly to be laid in an organic form like password under the field called ‘
No doubt there is a certain pattern — a certain adaptable method. Many start off by entering various scattered password into a single password-protected memo (the ‘piece of paper in the drawer’ equivalent). As experience develops, time takes its toll and scale becomes an issue. Passwords begin to migrate to the address book, possibly to be laid in an organic form like password under the field called ‘other‘ or ‘address‘ while the account name becomes just ‘name‘. In due time, even a single category in the address book does not suffice because of the ever-increasing number of accounts. Then, different categories for different passwords get created. This establishes layering, or a shallow hierarchy.
There is a huge advantage to this approach: when each and every record containing a password is marked ‘private‘, there is essentially one ‘master password’, much like a master key. The method rids you from the need to remember passwords. One password will unlock all others. It enables you to use a variety of different passwords without ever needing to memorise them.
Yet, as a final word of caution, records are not entirely safe on your computer (the PC-side). When you HotSync your data, this data is transfered and then stored unencrypted (in readable form) on your filesystem. Access to your hard-drive enabled access to your passwords, especially by a Palm-proficient intruder, perhaps an overly curious colleague. Having said that, the method fully protects your password in cases of PDA theft. I once came across all passwords of an MIT system administrator (while searching the Web for Tasks conversion tools) and informed him immediately so that he could empty corresponding Google cache. Needless to mention, he was frustrated and puzzled.
In summary, read the suggestions carefully and internalise what other people have learned from their mistakes. Be aware of the pitfalls and sensitivities of the method to intrusion. Lastly, never let your brain be consumed by a collection of crypic passwords. Remember just one master password.
Cited by: PalmAddict






 Filed under:
Filed under:  Tarring of files can handle the former task while the latter can have no positive effects (e.g. when compressing JPEG files that are already condensed). In some circumstances, the data being compressed is very light to begin with. Why compress it and lead to complications (indexing and searching, latency in opening files, re-ordering, etc.)? Why compress Web pages in Apache when there is still incomplete support by browsers? As regards databases, anybody whose textual content exceeds 10 MB is serious about Web development and thus will have plenty of server space to spare.
Tarring of files can handle the former task while the latter can have no positive effects (e.g. when compressing JPEG files that are already condensed). In some circumstances, the data being compressed is very light to begin with. Why compress it and lead to complications (indexing and searching, latency in opening files, re-ordering, etc.)? Why compress Web pages in Apache when there is still incomplete support by browsers? As regards databases, anybody whose textual content exceeds 10 MB is serious about Web development and thus will have plenty of server space to spare. The word on the street is that Microsoft’s CEO, Steve Ballmer, has lost a lot of weight recently. Perhaps he cannot sleep at night either, or perhaps, even more possibly, he is simply on a diet. I prefer to believe that he lost his appetite once he fully comprehended the fierce competition, which he reluctantly admitted to in a very recent interview on innovation (video in Windows-only WMV format, so see cocky
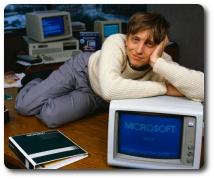
The word on the street is that Microsoft’s CEO, Steve Ballmer, has lost a lot of weight recently. Perhaps he cannot sleep at night either, or perhaps, even more possibly, he is simply on a diet. I prefer to believe that he lost his appetite once he fully comprehended the fierce competition, which he reluctantly admitted to in a very recent interview on innovation (video in Windows-only WMV format, so see cocky 
 edundancy makes computers much safer, more stable and more reliable than other aspects of our lives. Paper loss, theft — or more personally — physical damage, illness and other disastrous scenarios may be difficult to avoid. They all relate to the physical whereas information itself is metaphysical.
edundancy makes computers much safer, more stable and more reliable than other aspects of our lives. Paper loss, theft — or more personally — physical damage, illness and other disastrous scenarios may be difficult to avoid. They all relate to the physical whereas information itself is metaphysical. recently sought and discovered a plug-in for
recently sought and discovered a plug-in for 
 istory certainly repeats itself. Microsoft have once again imitated the user interface of the Mac, particularly the eye candy; their beta version clearly reflects on that. This beta was only announced a day or two ago, so the
istory certainly repeats itself. Microsoft have once again imitated the user interface of the Mac, particularly the eye candy; their beta version clearly reflects on that. This beta was only announced a day or two ago, so the  here comes a time in the lifecycle of an application when reliable and non-lossy export facilities need to be implemented. Unfortunately, ego of developers sometimes leads to good import facilities while there is only limited or no support for export of user data.
here comes a time in the lifecycle of an application when reliable and non-lossy export facilities need to be implemented. Unfortunately, ego of developers sometimes leads to good import facilities while there is only limited or no support for export of user data. 