Monday, December 12th, 2022, 7:45 am
Births in England and Wales Down 5.2% Since Pre-Pandemic Years, Baby Deaths Down by a Similar Level
Data for this article: Baby deaths [Open Document Format]
Hypothesis: babies born into the pandemic are equally likely to survive (but caveats exist, e.g. maybe only more affluent families still have kids and medical treatments continue to improve)
So I’ve decided to check how the pandemic affects babies, specifically people under the age of 1 in England and Wales, for which we have complete data from ONS.
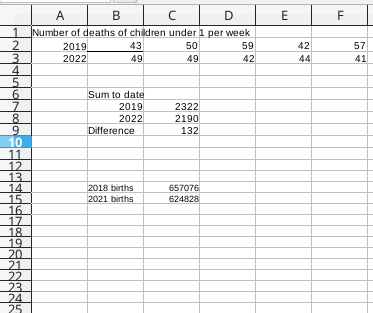
Based on the available data, 2,190 children under the age of 1 died so far this year, compared to 2,322 (132 more) in 2019. Those kids might be born a year earlier, i.e. in 2021 and in 2018.
Births in 2018 were 5.2% higher than in 2021, based on the official figures. 657,076 – 624,828 = 32,248 (fewer births in 2021 than in 2018), representing a big decrease.
Old data can be found here (births in England and Wales). It says: “There were 679,106 live births in England and Wales in 2017, a decrease of 2.5% from 2016 and the lowest number of live births since 2006.”
In 2018 there was a decrease. To quote: “There were 657,076 live births in England and Wales in 2018, a decrease of 3.2% since 2017 and a 9.9% decrease since the most recent peak in 2012.”
More recent data comes from this page (also see “Births by parents’ country of birth, England and Wales: 2021″). To quote: “There were 624,828 live births in England and Wales in 2021, an increase of 1.8% from 613,936 in 2020, but still below the 2019 figure (640,370); 2021 remains in line with the long-term trend of decreasing live births seen before the coronavirus (COVID-19) pandemic.”
It also says: “There were 2,597 stillbirths in 2021, an increase of 226 from 2020; this is similar to the 2,522 stillbirths in 2019. [..]. The stillbirth rate in 2021 increased to 4.1 stillbirths per 1,000 total births compared with 3.8 in 2020; this is also higher than the rate seen before the coronavirus pandemic in 2019 (3.9).”
Based on the available data, the number of babies dying in their first year was similar in the past year to what it was before the COVID-19 outbreak. If adjusted to the total number of births, compensating for disparity and assessing the ratio.
It may be safe to conclude that babies’ mortality rate (at least here) did not worsen in recent years, unlike all the other age groups.






 Filed under:
Filed under: